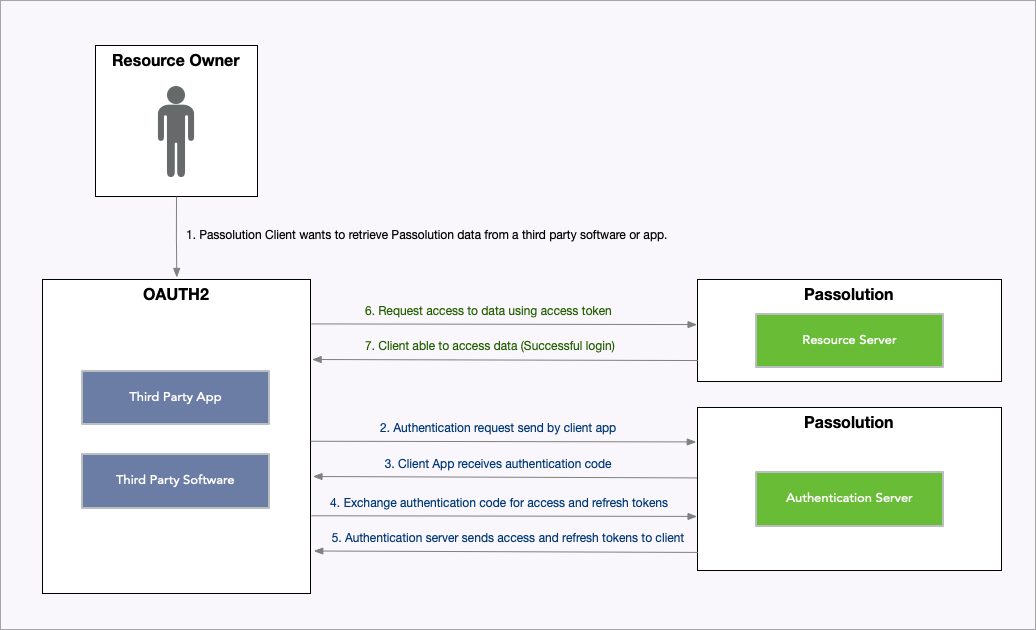
OAuth 2.0 Authentication
The Passolution Dataservice API uses the OAuth 2.0 protocol for authentication. It is an industry-standard protocol specification that enables third-party applications (clients) to gain delegated access to protected resources in the Passolution Dataservice via an API.
Why should we use OAuth 2.0?
Clients are not required to support password authentication or store user credentials.
Clients gain delegated access, i.e., access only to resources authenticated by the user.
Users can revoke the client's delegated access anytime.
OAuth 2.0 access tokens expire after a set time. If the client faces a security breach, user data will be compromised only until the access token is valid.
How OAuth 2.0 works?
Terminologies
The following are some terms you need to know before you start using the Passolution Dataservice APIs.
Protected resources
The Passolution Dataservice resources, such as Conditions, Entry, Visa, Transitvisa, Health, etc.
Resource server
The Passolution server that hosts protected resources.
Resource owner
Any end-user of your account, who can grant access to the protected resources.
Client
An application that sends requests to the resource server to access the protected resources on behalf of the end-user.
Client ID
The consumer key generated from the connected application.
Client Secret
The consumer secret generated from the connected application.
Authentication server
Authorization server provides the necessary credentials (such as Access and Refresh tokens) to the client. In this case, it will be the Passolution authorization server.
Authentication code
The authorization server creates a temporary token and sends it to the client via the browser. The client will send this code to the authorization server to obtain access and refresh tokens.
Tokens
Access Token
A token that is sent to the resource server to access the protected resources of the user. The Access token provides secure and temporary access to Passolution Dataservice APIs and is used by the applications to make requests to the connected app. Each access token will be valid only for an hour and can be used only for the set of operations that are described in the scope.
Refresh Token
A token that can be used to obtain new access tokens. This token has the same livetime as the token. A new token should be generated using the refresh token before the token expires.
User Access Token must be kept confidential since it defines the type of API that you use. Do NOT expose your Access Token anywhere in public forums, public repositories or on your website's client-side code like HTML or JavaScript. Exposing it to the public may lead to data theft, loss or corruption.